exynos8890-bootrom-dump : dump Exynos 8890 bootROM from Samsung Galaxy S7
Posted on Mon 15 June 2020 in Tool
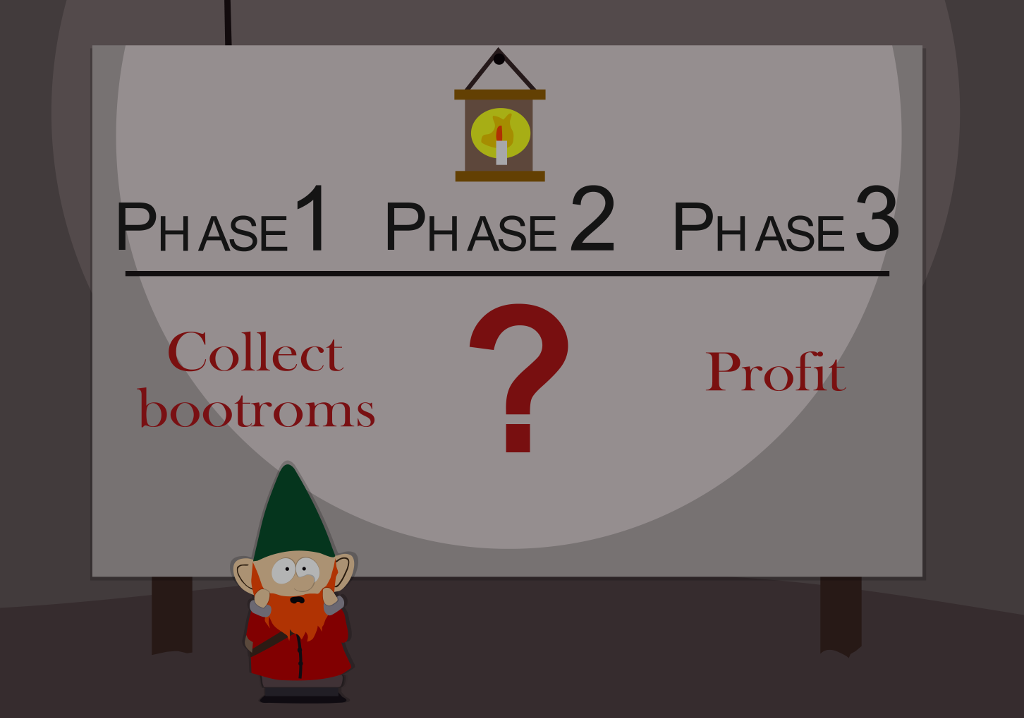
This post introduces a tool to dump Samsung Galaxy S7 bootROM using known and fixed security vulnerabilities in Trustzone.
The source code is available on GitHub.
Procedure
We use a Galaxy S7 phone, with ADB access and root privileges.
BootROM code is at address 0x0, in Secure world. The TEE (Trusted Execution Environment) running on this target is Trustonic Kinibi.
The approach is to escalate from Android to a Trusted driver and read secure memory at address 0x0.
We reuse fixed security bugs that are publicly documented. Two exploits are required, one to exploit a Trusted Application from Android, then a second to exploit a Trusted Driver. Both are simple stack overflow bugs. In both cases, return address is overwritten to redirect code execution to a ROP chain.
Trusted application exploitation
This part has been described by David Berard (p0ly) in very well-written article from Synacktiv. His work provides a very valuable starting point: an exploit for a Trusted Application with an example ROP chain.
We port the original exploit to our target (G930F), and then change the ROP chain. This new ROP chain calls the vulnerable Trusted Driver to deliver the second exploit.
Trusted driver exploitation
The second bug has been disclosed in a great talk from Quarkslab at BlackHat 2019. It is a trivial stack overflow due to memcpy operation, so exploiting it from the first ROP chain is straightforward.
The ROP chain we execute in the context of the Trusted Driver does the following operations :
- map physical address of bootROM
- map shared (secure & non-secure) buffer we initially allocated on Android side
- copy mapped bootROM to shared buffer
Finally, bootROM code is accessible to our Android executable.
Resources
This work has been possible thanks to the following previous research :